03.05.2022 - The NCSC received about the same number of reports last week as the week before. The investigation of attempted extortion with data from a hacked smartphone revealed that the cyberincident could be traced back to leaked login credentials. The leak in question occurred two years earlier at an alternative app store.

Last week, the NCSC was notified of a case where a smartphone was completely taken over by hackers, who gained access to the contacts, bank details and, of course, private photos. They then used this information to try to blackmail the owner of the phone.
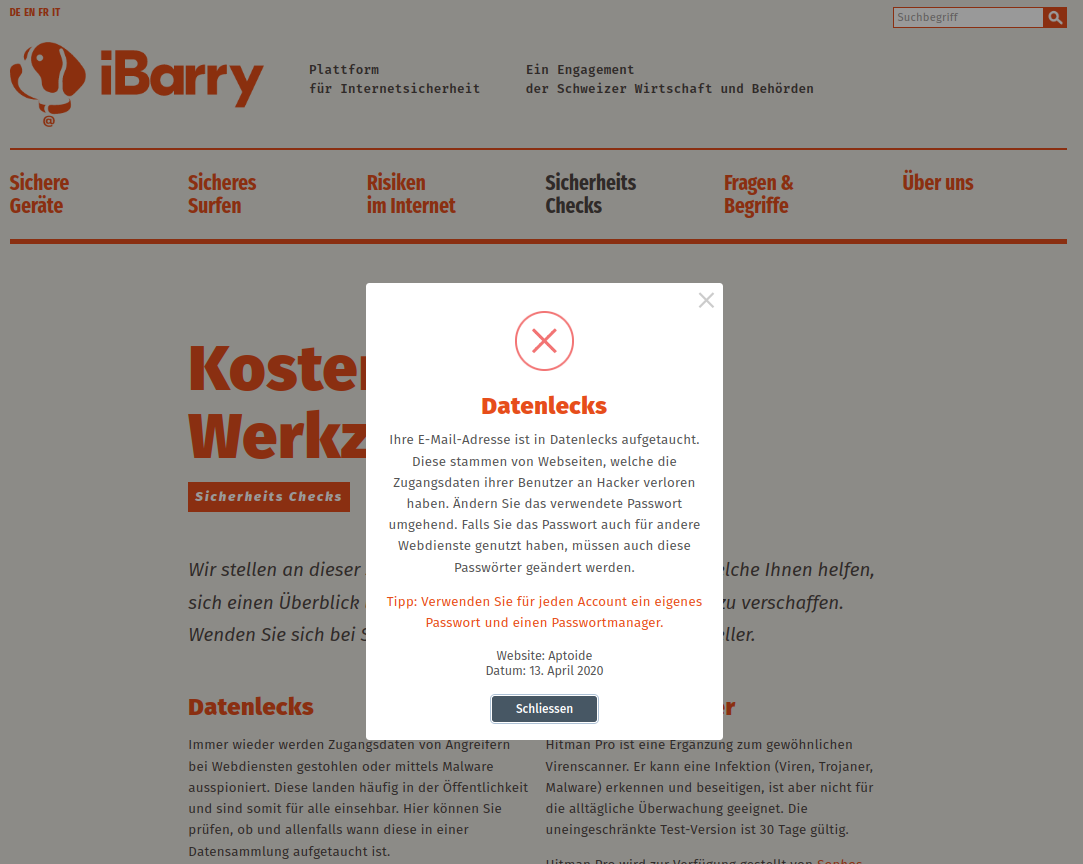
During the analysis, the NCSC discovered that the login credentials of the person who reported the case had been leaked. As a matter of fact, when the email address was checked, it turned out that the data had been leaked on the internet during a major data leak from the alternative app store Aptoide.
Aside from the app stores that are preinstalled on mobile phones by phone manufacturers (e.g. Google Play, Apple's App Store), other stores that offer apps also exist. These are called alternative or third-party app stores. While the official app store providers carry out in-depth checks on the apps, this is not the case with some alternative stores, or only to a limited extent. In addition, registration data stored there is particularly vulnerable, as it refers directly to the smartphones that have apps from the stores installed.
In the attack on the Aptoide app store, not only email addresses and user names were lost, but also passwords, IP addresses and information on the browser used. Since the passwords were not sufficiently protected, they can be reconstructed and used for attacks.
You should think carefully before using an alternative app store. In order to install an alternative app store, users have to grant some critical rights and are usually made aware several times that this can lead to security problems.
When alternative app stores are used, access to areas of the operating system that are normally blocked is enabled. In particular, the use of directly installable software (APK format, Android Application Package) which was not downloaded via an app store often results in a smartphone becoming infected. Those who use such methods should know exactly the risk to which they are exposing themselves and should thus trust the source. But apps from popular alternative app stores can also violate the rights granted to them without verification, e.g. in order to steal information.
Smartphones that have such software installed should never be used to conduct banking transactions or to store information that is intended solely for the user, e.g. passwords.
Recommendations on what to do:
- Check whether data related to your email addresses has been leaked online. You can find such a service on the iBarry website, for example, an initiative of the Swiss business community in cooperation with the cantonal police and the NCSC: https://www.ibarry.ch/en/security-checks/.
- If you are affected by a data leak, change the password associated with the email address wherever you have used it.
- Set up a separate email account with a secure password for smartphone registration and app stores, and use it solely for that app store.
- Only use alternative app stores if you are aware of the possible security problems and you trust the sources implicitly.
Current statistics
Last week's reports by category:
Last modification 03.05.2022