17.05.2022 - The NCSC again received about the same number of reports last week as the week before. Once more, text messages that attempted to trick victims into installing FluBot malware on their smartphones were observed. Attackers also used a devious method to try to hack into social media accounts. In addition, various variants for recovering allegedly stolen or blocked funds were observed.

Instagram is still my name
A particularly devious scam to hack an Instagram account was reported to the NCSC last week. The attackers targeted people who followed a famous person on social media and liked their posts. The fans, in this case fans of actor Terence Hill, were contacted by a supposed manager of the star and asked if they would like to write a short message to their idol's private Instagram account, which the fans could connect to. In order to "connect" the two accounts, the victims received a link that they were supposed to forward to the purported manager. As regular readers of our weekly review will already have guessed, the link was a password reset request. This gave the attackers the opportunity to reset the password and then log into the account. Subsequently, the email and telephone number stored were changed, thus blocking access for the victim.
- Do not send links or codes to people if you are asked to do so.
- Secure all your accounts, if possible using multi-factor authentication.
A blocked blockchain and recovered funds from fraud
The NCSC is increasingly receiving reports of purported organisations claiming to recover funds that have been fraudulently obtained and to "unblock" blockchains that have supposedly been frozen.
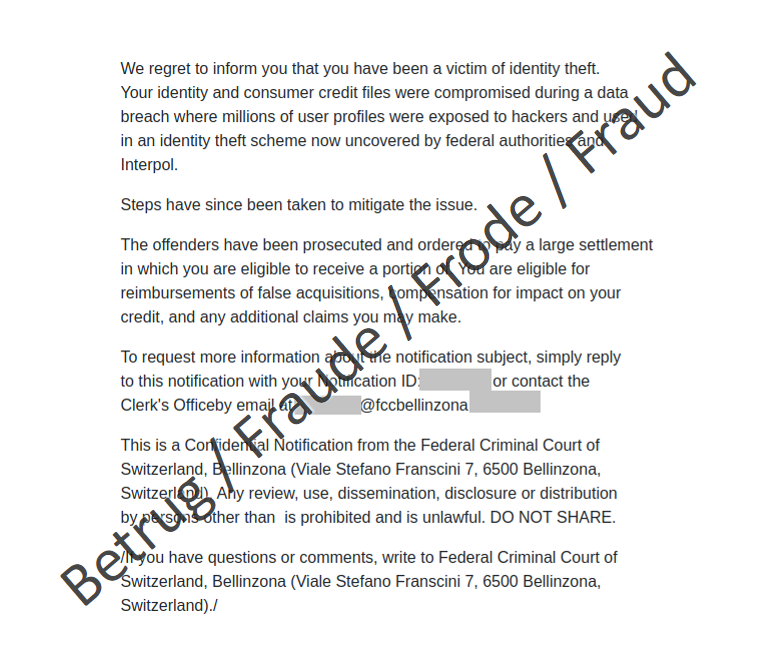
For example, an email specifically targeted at Swiss citizens purported to come from the Federal Criminal Court. The fraudsters registered specific domains for this purpose. These pose as the court and the communication takes place through them. The email informed the recipients that they were the victims of a large-scale identity theft. It stated that the perpetrators had been sentenced to a large fine and the victims were entitled to compensation. However, if the recipients contacted the address provided, fees were requested instead of compensation being paid. The promised compensation naturally does not exist.
In another case, a supposed consumer protection centre in Cyprus contacted people by phone and claimed that they had been the victim of a fraudulent broker and that a criminal investigation against the broker was in progress. The money had been frozen and the victims should now install remote desktop software and grant access to their computers in order to get their money back. This gave the attackers full access to the computers and they could then carry out any action they wanted.
Reports were also received of calls claiming that an amount of money was blocked on the blockchain. In these cases, too, a remote desktop app needed to be installed and access granted to the callers so that the funds could be released.
Recommendation:
- End such phone calls immediately. Neither Microsoft nor other software companies make unannounced or unsolicited support calls to resolve computer problems.
- Do not give anyone remote access to your computer.
- If you have granted remote access, there is a possibility that your computer has been infected. The first step is to uninstall the remote access program.
Current statistics
Last week's reports by category:
Last modification 17.05.2022