08.11.2022 - The number of reports received by the NCSC was once again up slightly on the previous week. In recent weeks, there has been a considerable jump in the number of reports submitted to the NCSC about hacked accounts for a wide range of online services. The damage caused by stolen login credentials can be greatly reduced by using different passwords and a password manager.

Hackers are increasingly attacking the online accounts of private individuals
Stolen passwords have been used for fake sextortion scams for some time now. The data is used as ostensible evidence to lend more credibility to the attacks. The NCSC reported on this in detail in weekla review 27.
However, the stolen data is now also being misused for other hacking activities. It is still unclear where the data originated. Both an extensive data leak from a hacked web service or login credentials from successful phishing campaigns are possible sources.
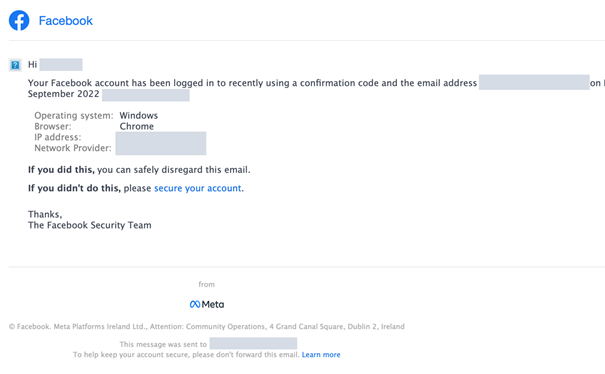
The hackers try to log in to social media accounts with the acquired data. If they succeed, they often upload pornographic material and have the accounts blocked afterwards, for example to support their hacking claim in the case of fake sextortion attacks. In other cases, the hackers attempt to hijack further accounts from the friends list or to lure people from the friends list into investment scams with "personalised" advertising.
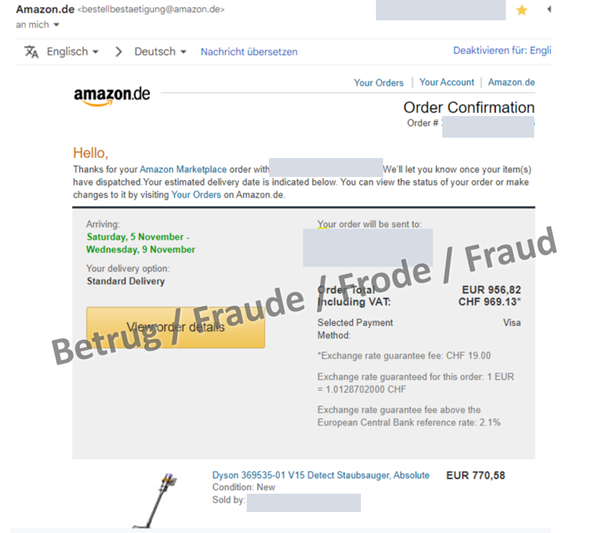
Moreover, the attackers try to log in to various online shops – phone providers, Amazon, Uber, airbnb, Netflix, Discord and Playstation are just some of the names cited in the reports received by the NCSC. If the hackers succeed in taking control of the email account, the passwords used can often be reset and the registered email address, sometimes even the phone number, can be changed. This means that the account is completely controlled by the hackers.
In one case reported to the NCSC, the hackers used the hijacked email account to create an Uber Eats account and have food delivered somewhere in South America. Stolen credit card details were used to pay. The same procedure had already been reported to the NCSC with Amazon accounts.
Protect accounts against hackers
If victims use the same password for several online services, hackers can hijack further services quite quickly. Therefore, using different passwords for each registration/service is an effective means of protection. Password managers such as KeePass, Keeper or Enpass can be used to manage the multitude of different passwords created as a result. The encrypted password database can be transferred between different devices. Cloud-based password managers likewise exist (e.g. SecureSafe, LastPass, 1Password and Bitwarden). Some browser manufacturers also offer solutions for securely exchanging online data between devices. However, the last two solutions are generally considered less secure than locally stored password data, as a security vulnerability or incorrect configuration could potentially make the password data accessible to third parties.
If your email provider offers two-factor authentication, you should definitely activate it.
Anyone who wants to be completely secure can consider using different email addresses for different purposes. This could include one email address for registering for various online services and another for communicating, for example.
Measures
- Do not reuse passwords: use a different password for each individual online service.
- Where possible, activate two-factor authentication: protect access to your internet services with two-factor authentication (one-time password, text message token, etc.) whenever available.
- Minimum length of 12 characters: passwords should be at least 12 characters long and contain lower and upper case letters, numbers and special characters.
- Change your password: you must change your password as soon as you suspect that it could be known to third parties.
- Use a password manager: you only need to remember the password to access the manager. Always keep an up-to-date copy of the password manager in a safe place.
Current statistics
Last week's reports by category:
Last modification 08.11.2022