09.05.2023 - Software updates are an integral part of computer security. However, cybercriminals also exploit this to install malware, as shown by an example reported to the NCSC last week. To convince victims to click on the link, the attackers also used information taken from leaked data.

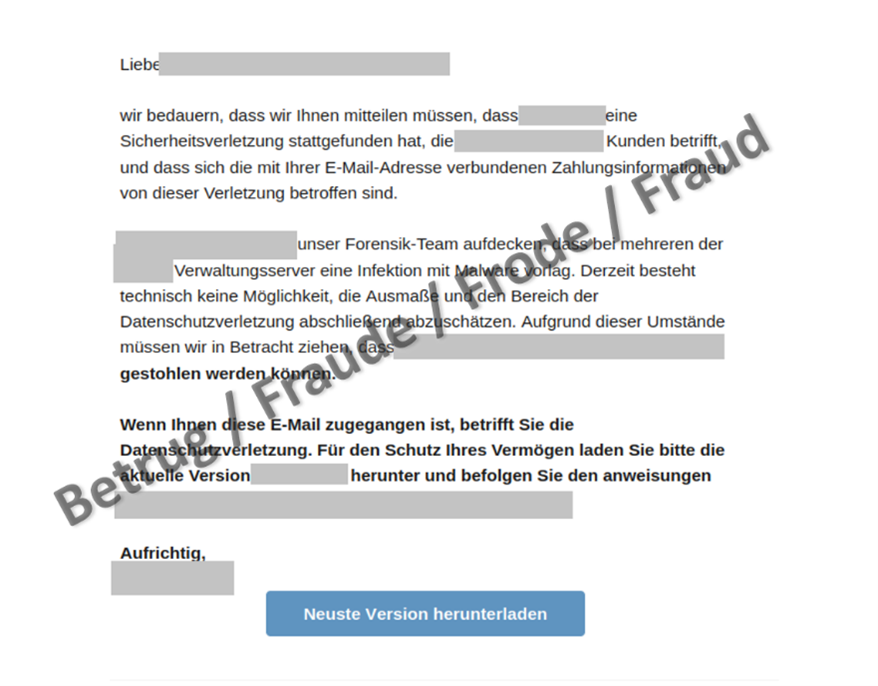
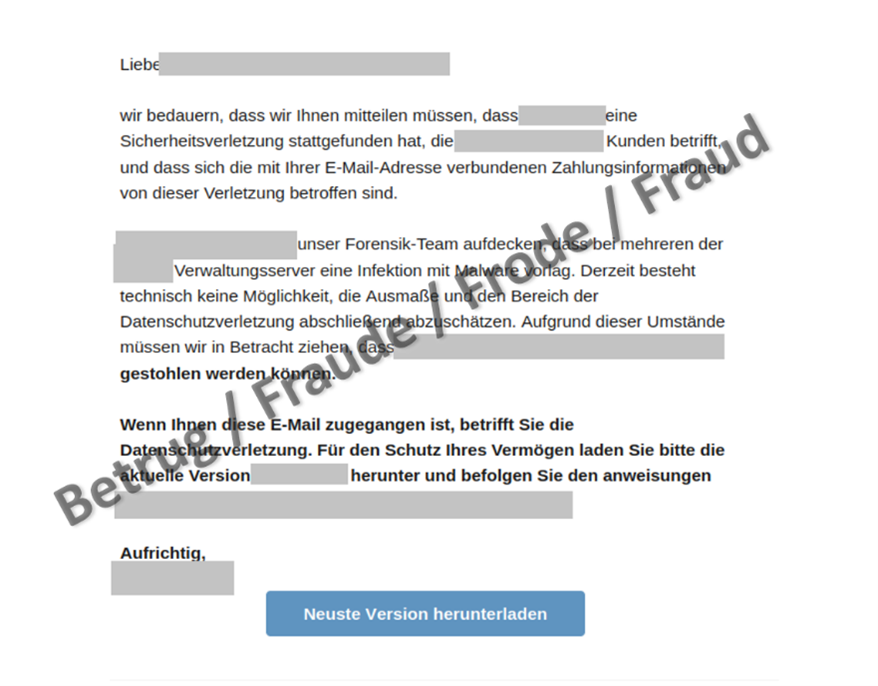
Email about an apparent security incident
In this case, the person who reported the case received an email from a company stating that a security breach had been detected and that various company servers had been infected with malware. This also concerned payment information and assets, which could be stolen as a result. The email claimed that it was necessary to install the latest financial software in order to protect the assets. To do so, the person who reported the case was told to click on the link and install the update provided.
The email contained a correct salutation and seemed trustworthy at first glance. The link was also very cunningly chosen, as only one letter differed from the original website. A victim therefore had to take a very close look to spot the scam. However, the whole story was fictitious. The company never had a security problem, and it was only when the update was installed that the software was manipulated in order to route network traffic via the fraudsters. This enabled the attackers to see and also manipulate the victims' data sent via the internet.
Was the email sent deliberately or on the off chance?
There is still the question of how the attackers could know which people were using the software. The email was sent to specific users rather than randomly. The use of the first name and surname in the salutation also suggests that the attackers possessed customer data. In actual fact, a look at the past showed that the company had experienced a data leak some time ago and that registration data from a newsletter had been leaked. Although the leak only involved names and email addresses, and not sensitive data such as passwords, the example shows that even data that seems worthless at first glance can be misused for further fraud. Criminals comb through leaked data for useful information, combine it with other data and then offer it for sale, thereby enabling highly targeted attacks under certain circumstances.
Consequently, it is very important for companies that are aware of a data leak to inform their customers promptly about the leak, even if no sensitive data is involved.
At the same time, internet users should periodically check whether data concerning their email addresses has been leaked on the internet. Such a service can be found on the iBarry website, for example, an initiative of the Swiss business community in cooperation with the cantonal police and the NCSC:
https://www.ibarry.ch/en/security-checks/.
Recommendations:
- While security updates are important, do not let your guard down. Take your time and check the website from which the update is to be downloaded.
- Do not install any software that you opened via a link in an email. Enter the address (URL) of the official provider manually in the address bar of your browser. If in doubt, ask the provider.
- Only download updates from the manufacturer's website.
- Personalised emails can be malicious too. If in doubt, ask the provider.
- If there is an automatic update function, activate it.
Current statistics
Last week's reports by category:
Last modification 09.05.2023