13.02.2024 - The NCSC frequently receives reports of hacked social media accounts or unknown online purchases. In many cases, the scam can be traced back to a hacked email account. Unfortunately, people tend to underestimate the importance of protecting their email accounts.

An online purchase you didn't make…
We regularly hear from people who receive an invoice for an order they didn't place. These orders are often for digital gift cards, for example. A fraudster can make use of the fact that they can simply be downloaded straight after the order is placed. They don't even need to be sent by post. This leaves the victim with a bill for something they didn't order – much less receive. To do this, the fraudster needs to have gained access to the victim's account for that online shop.
… or a hacked social media account
The NCSC also regularly hears from people whose social media accounts have been hacked. These accounts may then be used to send messages to known contacts, asking them for money under false pretences. Or they may be used to post fake ads. Unfortunately, regaining control of the social media account takes a lot of time and effort, and sometimes it's not even possible.
The hub
In many cases, social media accounts are attacked not directly but via a hacked email account. An email account can be a real treasure trove for attackers. It tells them all about the owner's daily life and reveals lots of information in the inbox, recycling bin and archive about accounts they may hold with service providers, social media platforms, online shops and other digital services. The attackers are usually quick to find the information they're looking for and can then use it as planned. Alternatively, they sell the victim's login credentials on the darknet.
The problem with resetting your password
A fraudster does not need to know an account's password in order to gain access: once they have email access, they just need to use the password reset function.
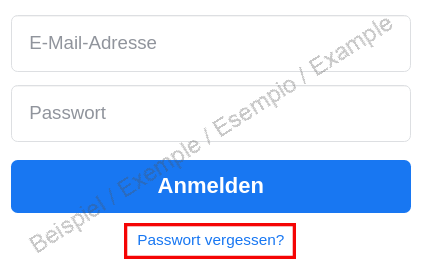
This either generates a new password or sends a link to reset the password. Both are conveniently sent to the very mailbox the fraudster has already hacked.
Clearly, a hacked email account can be worth a lot. All the hacker needs is the password – and there are several ways of getting this:
- The account holder may fall prey to a phishing attack and disclose the password voluntarily.
- The password may be too short or simple and easy for a hacker to guess or match against a password list.
Email/password combinations may be stolen in a data leak from an online service provider. Fraudsters will then try to access the email account with this password.
Precautions you should take
The NCSC recommends taking the following steps to protect your email account:
- Use a password of at least 12 characters, with a combination of uppercase and lowercase letters, numbers and special characters.
- Don't use the same password more than once.
- Use two-factor authentication (2FA). This adds an extra security step on top of your password, such as a numerical code that is generated and displayed in an authenticator app. 2FA is easy to use: you only have to set it up once, and usually you don't even have to enter the code each time – only if you log in on an unknown device. The second factor makes it much harder for someone to hack your account.
- You should only ever enter your email password in a webmail account (check the URL) or an email program on your PC and/or mobile phone. Never enter your password on a website you opened via a link in an email.
- If possible, use different email addresses for different purposes.
Further information is available on the NCSC website:
You can check for yourself whether your email address has ever been part of a (known) data leak on the 'Have I Been Pwned' project website (https://haveibeenpwned.com/). But don't be alarmed – the chances are that it has. What really matters is what other details were leaked along with the address. If your password has been compromised, the NCSC recommends you change it.
It's a good idea to check your email on another such tool, e.g. the Identity Leak Checker from the Hasso Plattner Institute in Potsdam, Germany. Even if one data leak checker does not flag your email as leaked, this does not mean it won't be flagged on another.
Current statistics
Last week's reports by category:
Last modification 13.02.2024





