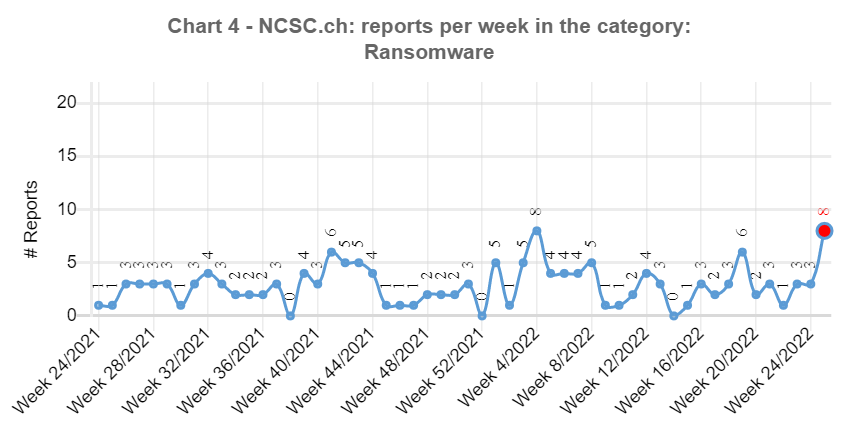
28.06.2022 - The NCSC again received a large number of reports last week. Eight reports on encryption Trojans, also known as ransomware, remind us how important it is to take precautions to protect ourselves from such attacks.

Ransomware – precautions are important
After five weeks of relatively low numbers of reported ransomware incidents, eight cases were reported to the NCSC last week. The astonishing thing was that practically every case involved a different malware; the NCSC received reports concerning Sodinokibi, Lockbit 2.0, Conti, Black.Basta and Deadbolt.
Although eight reports seems insignificant at first glance, the damage caused by ransomware attacks is usually very significant. Even if a functioning backup exists and the data can be restored, the systems are not available or only partially available for a few days, which leads to a corresponding loss of production. In addition, attackers often have a plan B ready in case the victims have taken precautions for the event that their data is lost and therefore have an up-to-date data backup that can be used. To make sure that they still receive their ransom, attackers specialise in copying the data before it is encrypted and then threatening to publish it (double extortion). Things become even more problematic if the attackers also manage to encrypt the backups and there is no way to restore the data. In such cases, a company's very existence can be at stake.
Protective measures
Protective measures against cyberattacks must be taken in advance. As shown in weekly reviews 23 and 24, it is important that systems be kept up to date and that access to web services and email accounts be secured using two-factor authentication. Furthermore, special attention should be paid to all VPN connections. It is also important that companies regularly train their employees on cybersecurity, especially how to deal with emails.
The risk of a ransomware incident can be minimised in this way, but a residual risk always remains. Therefore, further preparatory organisational measures must be taken in case of an attack. These include the creation and regular testing of offline backups, but also establishing contacts with security service providers who can handle such an incident and a communication strategy that comes into play in the event that internal company data is published. This is referred to as an incident response plan. This should contain all important tasks, instructions and contact details and must be available in hard copy.
A list of preventive measures to protect against ransomware can be found at:
In the event of a ransomware incident, instructions on how to proceed are listed on the following website:
Current statistics
Last week's reports by category:
Last modification 28.06.2022





