19.09.2023 - In recent months, cybercriminals have come up with a variety of fake support scams that are aimed at installing a remote access tool on the victim's computer and then making credit card payments or e-banking transactions.

Callers pretending to be an employee of an IT company, and claiming that the victim's computer is infected and needs to be repaired, have been around for some time. The fake support callers phone people at random. They have no idea how the computers of the people they are calling are configured. The attackers' main objective is to persuade the victims to download a program (remote access tool) that allows them to access the computer, which provides them with a gateway for further criminal activity. Recent months have seen the arrival of two new variants, which ultimately turn out to also be fake support scams. Perhaps the original IT support scam is not as lucrative as it used to be, or the victims have become more sceptical and thus more careful, so the perpetrators are trying other tactics.
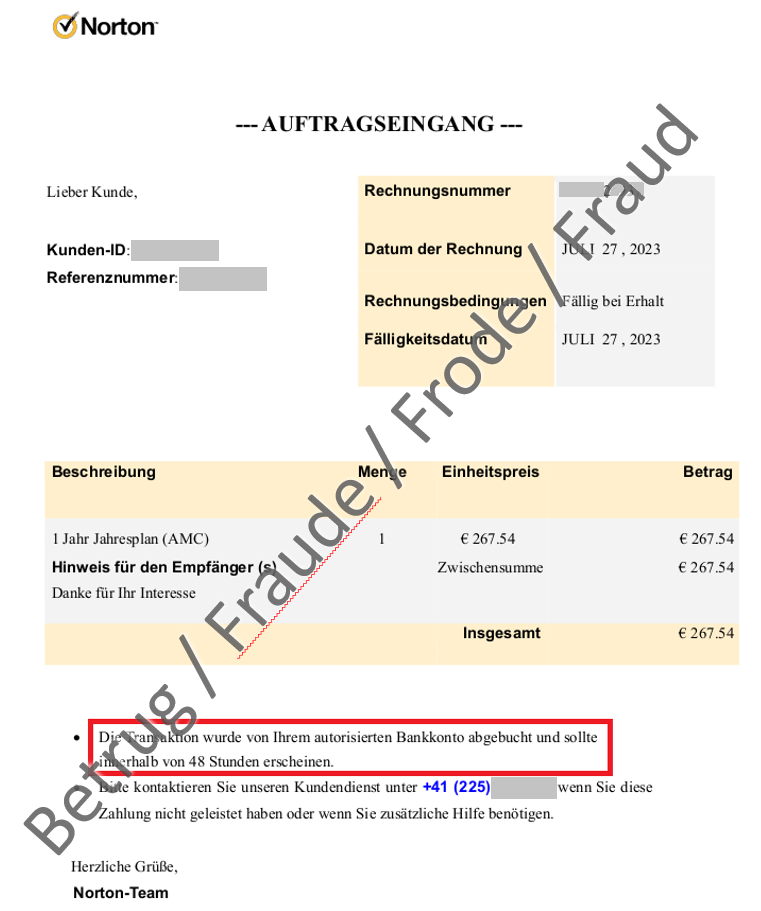
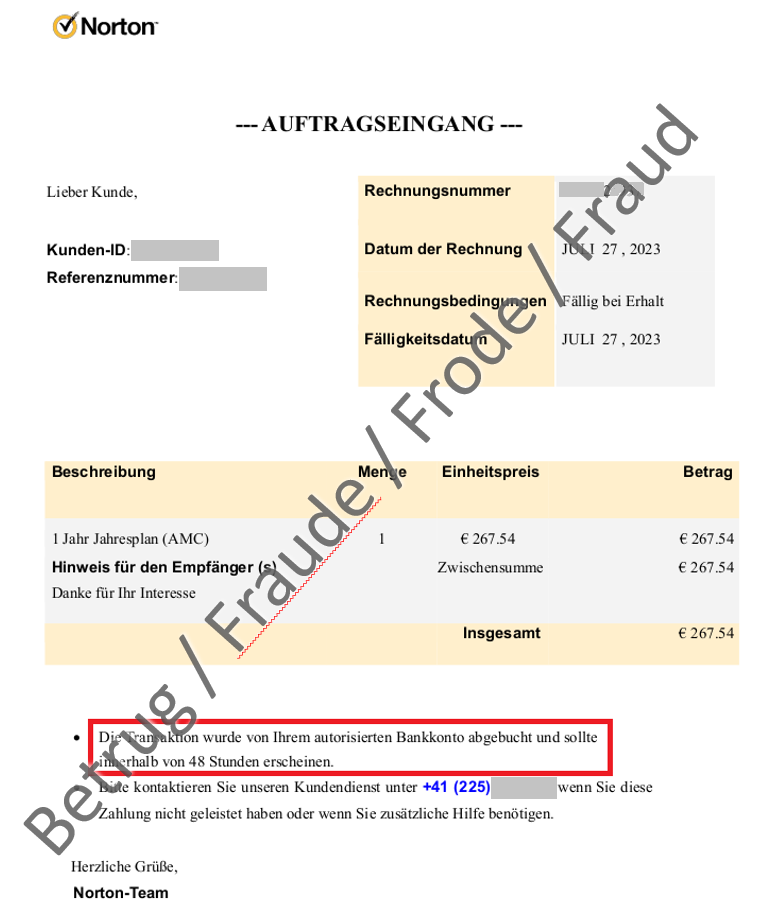
Fake invoices
In the first variant, the fraudsters claim that the victim has bought something, and send them a fake invoice. In most cases, the supposed purchase involves a subscription for an antivirus program. The invoice in the mail appears to show that the victim has already paid the bill. The recipient is told to contact the invoicing party if they do not agree with the payment. A phone number is given as the only way of contacting the invoicing party. In order to ensure that the victim does not get suspicious, the numbers given are usually Swiss numbers. If the victim calls the number, they are connected to a call centre employee who promises to solve the problem immediately. The customer is told to install a remote access tool on their computer, so that the "employee" can cancel the payment. Once the remote access tool is installed, the customer is supposed to enter their access credentials for the e-banking portal or their credit card details. The fraudsters then make various payments in the background.
Fake calls from the police
Since the end of June, the NCSC has been receiving a large number of reports about the second variant. This starts with an apparent phone call from the police. A computer-generated voice informs the victim that their personal banking data has been brought into connection with a crime. For further information, the call recipient should press 1. The modus operandi was initially unclear, but the reports by members of the public indicate that in the case of a call back, the victim is told to download a remote access tool and grant the attackers access to their computer. Here too, the fraudsters try to persuade the victim to grant access to their e-banking account. Once the fraudsters have obtained access, they use the remote access tool to make payments in the background.
- End such phone calls immediately.
- If you provided credit card details, contact your credit card company immediately to have the card blocked.
- If you made a payment, immediately contact the bank through which you made it. They may be able to stop the payment.
- Do not give anyone remote access to your computer. If you granted remote access, there is a possibility that your computer has been infected. The first step is to uninstall the remote access program. If you suspect an infection, have your computer examined immediately by a specialist and cleaned if necessary. The safest option is to completely reinstall the computer. However, do not forget to back up all personal data beforehand.
Current statistics
Last week's reports by category:
Last modification 18.09.2023